Question 19
A high-usage cloud resource needs to be monitored in real time on specific events to guarantee its availability. Which of the following actions should be used to meet this requirement?
Correct Answer:B
To guarantee real-time monitoring of a high-usage cloud resource, creating a dashboard with visualizations to filter the status of critical activities is effective. This allows for a quick visual assessment of the system's health and performance, enabling immediate action if specific events indicate potential issues with availability.References: Real-time monitoring and the use of dashboards for tracking critical cloud resources are part of the cloud management best practices covered under the CompTIA Cloud+ objectives.
Question 20
A developer is deploying a new version of a containerized application. The DevOps team wants:
• No disruption
• No performance degradation
* Cost-effective deployment
• Minimal deployment time
Which of the following is the best deployment strategy given the requirements?
Correct Answer:C
The blue-green deployment strategy is the best given the requirements for no disruption, no performance degradation, cost-effective deployment, and minimal deployment time. It involves maintaining two identical production environments (blue and green), where one hosts the current application version and the other is used to deploy the new version. Once testing on the green environment is complete, traffic is switched from blue to green, ensuring a seamless transition with no downtime.References: Understanding various cloud deployment strategies, such as blue-green deployments, is essential for managing cloud environments effectively, as highlighted in the CompTIA Cloud+ objectives, to ensure smooth and efficient application updates.
Question 21
A cloud engineer is in charge of deploying a platform in an laaS public cloud. The application tracks the state using session cookies, and there are no affinity restrictions.
Which of the following will help the engineer reduce monthly expenses and allow the application to provide the service?
Correct Answer:D
A pay-as-you-go model would be beneficial for the cloud engineer because it allows the application to be scaled based on demand, reducing monthly expenses since costs are only incurred for the resources actually used. Since there are no affinity restrictions and the application uses session cookies for state tracking, the pay-as-you-go model can handle fluctuating workloads without the need to pay for unused reserved resources or dedicated hosts. References: CompTIA Cloud+ Study Guide (Exam CV0-004) - Chapter on Cloud Service Models
Question 22
A newly configured VM fails to run application updates despite having internet access. The updates download automatically from a third-party network. Given the following output: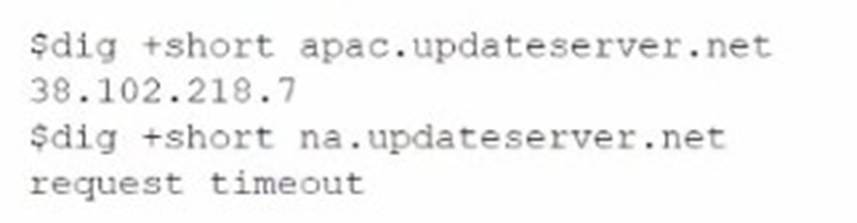
Which of the following troubleshooting steps would be best to take?
Correct Answer:A
The best troubleshooting step to take given the output is to check DNS configurations. The failure to resolve the "na.updateserver.net" domain suggests a DNS resolution issue, which could be due to incorrect DNS settings, a failure in the DNS service, or an issue with the DNS server itself.References: Troubleshooting DNS issues is a crucial skill in cloud management, as DNS plays a fundamental role in network connectivity and access to resources. It is covered under Cloud Concepts in the CompTIA Cloud+ curriculum.
Question 23
A security engineer Identifies a vulnerability m a containerized application. The vulnerability can be exploited by a privileged process to read tie content of the host's memory. The security engineer reviews the following Dockerfile to determine a solution to mitigate similar exploits:
Which of the following is the best solution to prevent similar exploits by privileged processes?
Correct Answer:A
Adding the "USER myappuser" instruction to the Dockerfile is the best solution to prevent similar exploits by privileged processes. This instruction ensures that the container runs as a non-privileged user instead of the root user, significantly reducing the risk of privileged exploits. Running containers with least privilege principles minimizes the potential impact of vulnerabilities, enhancing the overall security posture of the containerized environment.References: The CompTIA Cloud+ framework includes security concerns, measures, and concepts for cloud operations, highlighting the importance of container security practices, such as running containers as non-root users to prevent unauthorized access and exploitation.
Question 24
A list of CVEs was identified on a web server. The systems administrator decides to close the ports and disable weak TLS ciphers. Which of the following describes this vulnerability management stage?
Correct Answer:D
Closing the ports and disabling weak TLS ciphers as a response to a list of identified CVEs (Common Vulnerabilities and Exposures) describes the vulnerability management stage of 'remediation'. This stage involves taking actions to resolve vulnerabilities and mitigate potential risks.References: Vulnerability management stages, including remediation efforts, are a key aspect of the security measures discussed in CompTIA Cloud+.