Online FCP_FCT_AD-7.4 Practice TestMore Fortinet Products >
Free Fortinet FCP_FCT_AD-7.4 Exam Dumps Questions
Fortinet FCP_FCT_AD-7.4: FCP - FortiClient EMS 7.4 Administrator
- Get instant access to FCP_FCT_AD-7.4 practice exam questions
- Get ready to pass the FCP - FortiClient EMS 7.4 Administrator exam right now using our Fortinet FCP_FCT_AD-7.4 exam package, which includes Fortinet FCP_FCT_AD-7.4 practice test plus an Fortinet FCP_FCT_AD-7.4 Exam Simulator.
- The best online FCP_FCT_AD-7.4 exam study material and preparation tool is here.
Question 1
An administrator deploys a FortiClient installation through the Microsoft AD group policy After installation is complete all the custom configuration is missing.
What could have caused this problem?
Correct Answer:D
Question 2
What action does FortiClient anti-exploit detection take when it detects exploits?
Correct Answer:B
Question 3
Which three features does FortiClient endpoint security include? (Choose three.)
Correct Answer:BDE
Question 4
Refer to the exhibit, which shows the output of the ZTNA traffic log on FortiGate.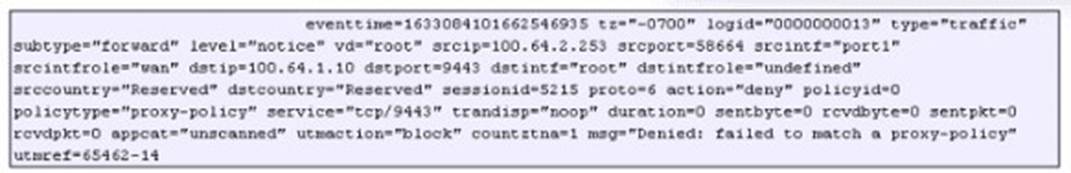
What can you conclude from the log message?
Correct Answer:B
Question 5
Refer to the exhibit.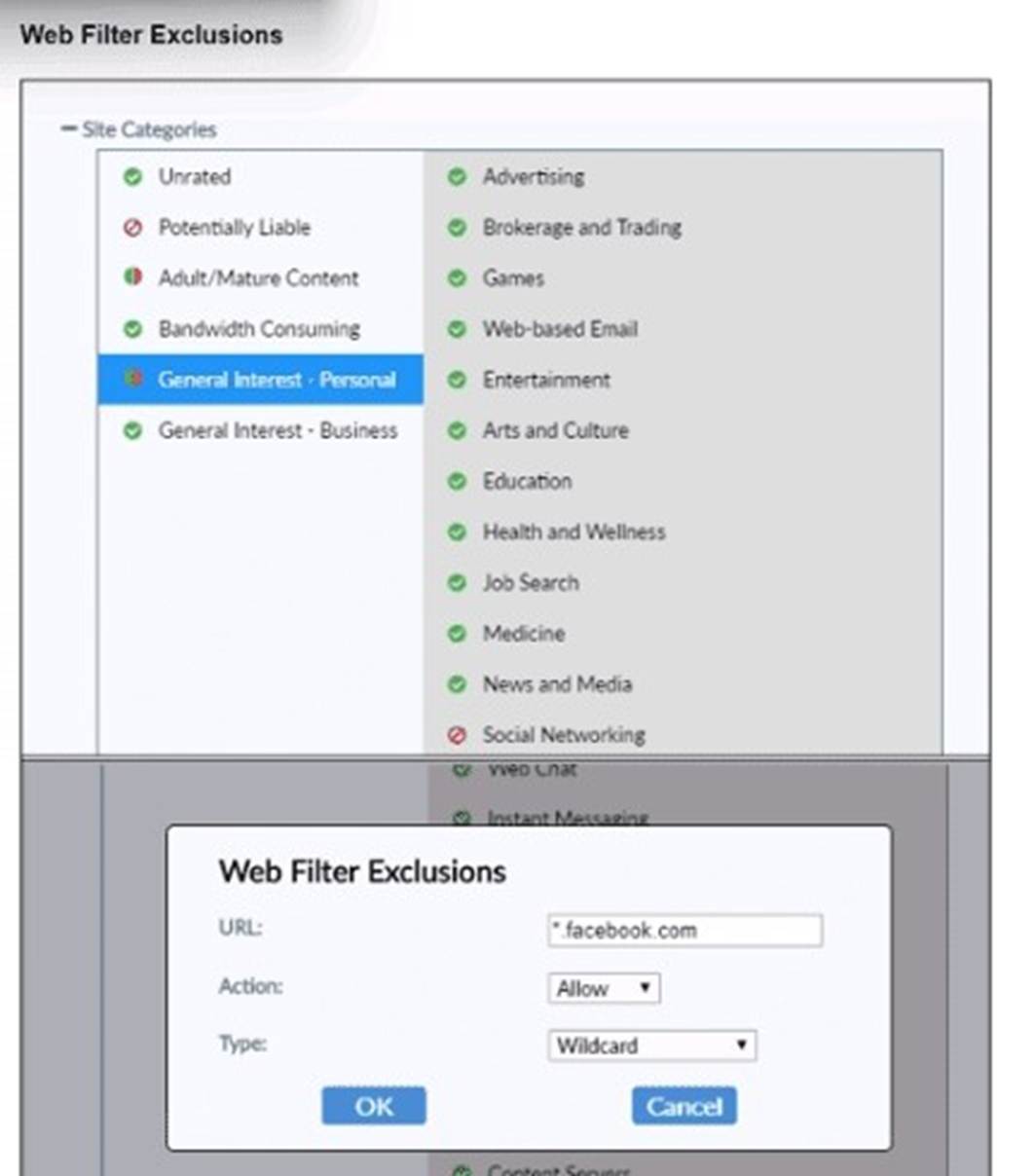
Based on the settings shown in the exhibit, which action will FortiClient take when users try to access www facebook com?
Correct Answer:B
Question 6
An administrator must deploy FortiClient for an organization that has BYOD and remote users.
What can the administrator use to deploy FortiClient? (Choose one answer)
Correct Answer:C