Question 55
- (Topic 1)
Study the snort rule given below: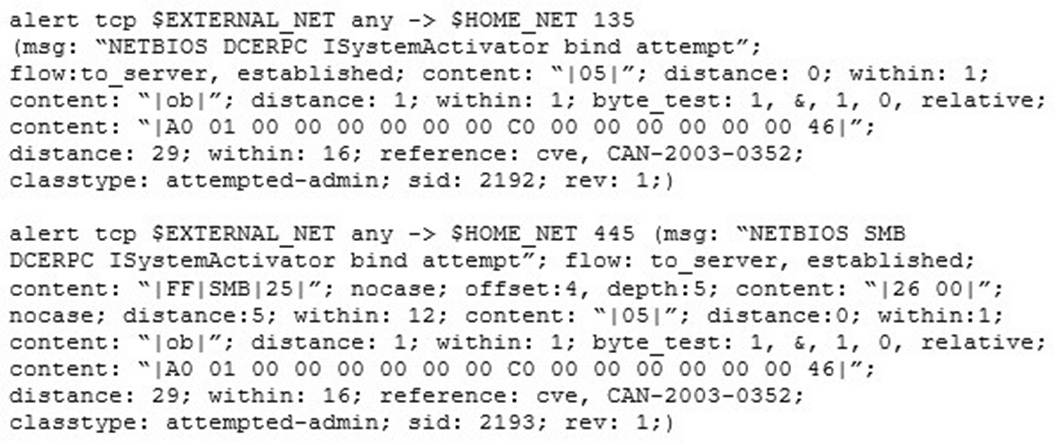
From the options below, choose the exploit against which this rule applies.
Correct Answer:C
Question 56
- (Topic 2)
A pen tester is configuring a Windows laptop for a test. In setting up Wireshark, what river and library
are required to allow the NIC to work in promiscuous mode?
Correct Answer:D
Question 57
- (Topic 3)
Geena, a cloud architect, uses a master component in the Kubernetes cluster architecture that scans newly generated pods and allocates a node to them. This component can also assign nodes based on factors such as the overall resource requirement, data locality, software/hardware/policy restrictions, and internal workload interventions.
Which of the following master components is explained in the above scenario?
Correct Answer:B
Question 58
- (Topic 3)
A penetration tester is tasked with gathering information about the subdomains of a target organization's website. The tester needs a versatile and efficient solution for the task. Which of the following options would be the most effective method to accomplish this goal?
Correct Answer:A
Employing a tool like Sublist3r, which is designed to enumerate the subdomains of websites using OSINT, would be the most effective method to accomplish this goal. This option works as follows:
✑ Sublist3r is a python tool designed to enumerate subdomains of websites using
OSINT (Open Source Intelligence). It helps penetration testers and bug hunters collect and gather subdomains for the domain they are targeting. Sublist3r enumerates subdomains using many search engines such as Google, Yahoo, Bing, Baidu, and Ask. Sublist3r also enumerates subdomains using Netcraft, Virustotal, ThreatCrowd, DNSdumpster, and ReverseDNS. Subbrute was integrated with Sublist3r to increase the possibility of finding more subdomains using bruteforce with an improved wordlist1.
✑ By using Sublist3r, the tester can quickly and efficiently discover the subdomains
of the target organization??s website, which can provide valuable information about the network structure, the services offered, the potential vulnerabilities, and the attack surface. Sublist3r can also be used to perform passive reconnaissance, which does not send any packets to the target domain, and thus avoids detection by the target organization12.
The other options are not as effective as option A for the following reasons:
✑ B. Analyzing Linkedin profiles to find employees of the target company and their job titles: This option is not relevant because it does not address the subdomain enumeration task, but the social engineering task. Linkedin is a social networking platform that allows users to create and share their professional profiles, which may include their name, job title, company, skills, education, and contacts. By analyzing Linkedin profiles, the tester may be able to find employees of the target company and their job titles, which can be useful for crafting phishing emails, impersonating employees, or exploiting human weaknesses. However, this option does not help to discover the subdomains of the target organization??s website, which is the goal of this scenario3.
✑ C. Utilizing the Harvester tool to extract email addresses related to the target domain using a search engine like Google or Bing: This option is not sufficient because it does not provide a comprehensive list of subdomains, but only a partial list based on email addresses. The Harvester is a tool that can extract email addresses, subdomains, hosts, employee names, open ports, and banners from different public sources, such as search engines, PGP key servers, and SHODAN computer database. By using the Harvester, the tester may be able to extract
some email addresses related to the target domain, which can reveal some subdomains, such as mail.target.com or support.target.com. However, this option does not guarantee to find all the subdomains of the target organization??s website, as some subdomains may not have any email addresses associated with them, or may not be indexed by the search engines4.
✑ D. Using a people search service, such as Spokeo or Intelius, to gather
information about the employees of the target organization: This option is not applicable because it does not address the subdomain enumeration task, but the personal information gathering task. Spokeo and Intelius are people search services that can provide various information about individuals, such as their name, address, phone number, email, social media, criminal records, and financial history. By using these services, the tester may be able to gather information about the employees of the target organization, which can be useful for performing
background checks, identity theft, or blackmail. However, this option does not help to discover the subdomains of the target organization??s website, which is the goal
of this scenario56. References:
✑ 1: GitHub - aboul3la/Sublist3r: Fast subdomains enumeration tool for penetration testers
✑ 2: Subdomain Discovery in Cybersecurity with Kali Linux | Medium
✑ 3: LinkedIn - Wikipedia
✑ 4: The Harvester - Kali Linux Tools
✑ 5: Spokeo - Wikipedia
✑ 6: Intelius - Wikipedia
Question 59
- (Topic 2)
which of the following information security controls creates an appealing isolated environment for hackers to prevent them from compromising critical targets while simultaneously gathering information about the hacker?
Correct Answer:B
A honeypot may be a trap that an IT pro lays for a malicious hacker, hoping that they will interact with it during a way that gives useful intelligence. It??s one among the oldest security measures in IT, but beware: luring hackers onto your network, even on an isolated system, are often a dangerous game.honeypot may be a good starting place: ??A honeypot may be a computer or computing system intended to mimic likely targets of cyberattacks.?? Often a honeypot are going to be deliberately configured with known vulnerabilities in situation to form a more tempting or obvious target for attackers. A honeypot won??t contain production data or participate in legitimate traffic on your network
— that??s how you??ll tell anything happening within it??s a results of an attack. If someone??s stopping by, they??re up to no good.That definition covers a various array of systems, from bare-bones virtual machines that only offer a couple of vulnerable systems to ornately constructed fake networks spanning multiple servers. and therefore the goals of these who build honeypots can vary widely also , starting from defense thorough to academic research. additionally , there??s now an entire marketing category of deception technology that, while not meeting the strict definition of a honeypot, is certainly within the same family. But we??ll get thereto during a moment.honeypots aim to permit close analysis of how hackers do their dirty work. The team controlling the honeypot can watch the techniques hackers use to infiltrate systems, escalate privileges, and otherwise run amok through target networks. These sorts of honeypots are found out by security companies, academics, and government agencies looking to look at the threat landscape. Their creators could also be curious about learning what kind of attacks are out there, getting details on how specific sorts of attacks work, or maybe trying to lure a specific hackers within the hopes of tracing the attack back to its source. These systems are often inbuilt fully isolated lab environments, which ensures that any breaches don??t end in non-honeypot machines falling prey to attacks.Production honeypots, on the opposite hand, are usually deployed in proximity to some organization??s production infrastructure, though measures are taken to isolate it the maximum amount as possible. These honeypots often serve both as bait to distract hackers who could also be trying to interrupt into that organization??s network, keeping them faraway from valuable data or services; they will also function a canary within the coalpit , indicating that attacks are underway and are a minimum of partially succeeding.
Question 60
- (Topic 3)
A security analyst is preparing to analyze a potentially malicious program believed to have infiltrated an organization's network. To ensure the safety and integrity of the production environment, the analyst decided to use a sheep dip computer for the analysis. Before initiating the analysis, what key step should the analyst take?
Correct Answer:B
A sheep dip computer is a dedicated device that is used to test inbound files or physical media for viruses, malware, or other harmful content, before they are allowed to be used with other computers. The term sheep dip comes from a method of preventing the spread of parasites in a flock of sheep by dipping the new animals that farmers are adding to the flock in a trough of pesticide. A sheep dip computer is isolated from the organization??s network and has port monitors, file monitors, network monitors, and antivirus software installed. Before initiating the analysis of a potentially malicious program, the analyst should store the program on an external medium, such as a CD-ROM, and then insert it into the sheep dip computer. This way, the analyst can prevent the program from infecting other devices or spreading over the network, and can safely analyze its behavior and characteristics.
The other options are not correct steps to take before initiating the analysis. Running the potentially malicious program on the sheep dip computer may cause irreversible damage to the device or compromise its security. Connecting the sheep dip computer to the organization??s internal network may expose the network to the risk of infection or attack. Installing the potentially malicious program on the sheep dip computer may not be possible or advisable, as the program may require certain dependencies or permissions that the sheep dip computer does not have or allow. References:
✑ Sheep dip (computing)
✑ What Does ??Sheep Dip?? Mean in Cyber Security?
✑ Malware Analysis
✑ What is a Sheepdip?