Question 43
- (Topic 1)
Which of the following is not a Bluetooth attack?
Correct Answer:A
https://github.com/verovaleros/bluedriving
Bluedriving is a bluetooth wardriving utility. It can capture bluetooth devices, lookup their services, get GPS information and present everything in a nice web page. It can search for and show a lot of information about the device, the GPS address and the historic location of devices on a map. The main motivation of this tool is to research about the targeted surveillance of people by means of its cellular phone or car. With this tool you can capture information about bluetooth devices and show, on a map, the points where you have seen the same device in the past.
Question 44
- (Topic 2)
Clark, a professional hacker, was hired by an organization lo gather sensitive Information about its competitors surreptitiously. Clark gathers the server IP address of the target organization using Whole footprinting. Further, he entered the server IP address as an input to an online tool to retrieve information such as the network range of the target organization and to identify the network topology and operating system used in the network. What is the online tool employed by Clark in the above scenario?
Correct Answer:B
https://search.arin.net/rdap/?query=199.43.0.43
Question 45
- (Topic 2)
Which file is a rich target to discover the structure of a website during web-server footprinting?
Correct Answer:B
Information Gathering from Robots.txt File A website owner creates a robots.txt file to list the files or directories a web crawler should index for providing search results. Poorly written robots.txt files can cause the complete indexing of website files and directories. If confidential files and directories are indexed, an attacker may easily obtain information such as passwords, email addresses, hidden links, and membership areas. If the owner of the target website writes the robots.txt file without allowing the indexing of restricted pages for providing search results, an attacker can still view the robots.txt file of the site to
discover restricted files and then view them to gather information. An attacker types URL/robots.txt in the address bar of a browser to view the target website??s robots.txt file. An attacker can also download the robots.txt file of a target website using the Wget tool. Certified Ethical Hacker(CEH) Version 11 pg 1650
Question 46
- (Topic 3)
During a reconnaissance mission, an ethical hacker uses Maltego, a popular footprinting tool, to collect information about a target organization. The information includes the target's Internet infrastructure details (domains, DNS names, Netblocks, IP address information).
The hacker decides to use social engineering techniques to gain further information. Which of the following would be the least likely method of social engineering to yield beneficial information based on the data collected?
Correct Answer:A
Shoulder surfing is a social engineering technique that involves looking over someone??s shoulder to observe sensitive information, such as passwords, PINs, or credit card numbers, that they enter on their computer, phone, or ATM. It is the least likely method of social engineering to yield beneficial information based on the data collected by Maltego, because it requires physical proximity and access to the target??s devices, which may not be feasible or safe for the hacker. Moreover, shoulder surfing does not leverage the information obtained by Maltego, such as domains, DNS names, Netblocks, or IP addresses, which are more relevant for network-based attacks.
The other options are more likely to yield beneficial information based on the data collected by Maltego, because they involve exploiting the target??s trust, curiosity, or negligence, and using the information obtained by Maltego to craft convincing scenarios or messages. Impersonating an ISP technical support agent to trick the target into providing further network details is a form of pretexting, where the hacker creates a false identity and scenario to obtain information or access from the target. Dumpster diving in the target company??s trash bins for valuable printouts is a technique that relies on the target??s negligence or lack of proper disposal of sensitive documents, such as network diagrams, passwords, or confidential reports. Eavesdropping on internal corporate conversations to understand key topics is a technique that exploits the target??s curiosity or lack of awareness, and allows the hacker to gather information about the target??s projects, plans, or problems, which can be used for further attacks or extortion. References:
✑ Social Engineering: Definition & 5 Attack Types
✑ How to Use Maltego Transforms to Map Network Infrastructure: An In-Depth Guide
✑ Social engineering: Definition, examples, and techniques
Question 47
- (Topic 2)
what is the port to block first in case you are suspicious that an loT device has been compromised?
Correct Answer:C
TCP port 48101 uses the Transmission management Protocol. transmission control protocol is one in all the most protocols in TCP/IP networks. transmission control protocol could be a connection-oriented protocol, it needs acknowledgement to line up end- to-end communications. only a association is about up user??s knowledge may be sent bi- directionally over the association.
Attention! transmission control protocol guarantees delivery of knowledge packets on port 48101 within the same order during which they were sent. bonded communication over transmission control protocol port 48101 is that the main distinction between transmission control protocol and UDP. UDP port 48101 wouldn??t have bonded communication as transmission control protocol.
UDP on port 48101 provides Associate in Nursing unreliable service and datagrams might arrive duplicated, out of order, or missing unexpectedly. UDP on port 48101 thinks that error checking and correction isn??t necessary or performed within the application, avoiding the overhead of such process at the network interface level.
UDP (User Datagram Protocol) could be a borderline message-oriented Transport Layer protocol (protocol is documented in IETF RFC 768).
Application examples that always use UDP: vocalisation IP (VoIP), streaming media and period multiplayer games. several internet applications use UDP, e.g. the name System (DNS), the Routing info Protocol (RIP), the Dynamic Host Configuration Protocol (DHCP), the straightforward Network Management Protocol (SNMP).
Question 48
- (Topic 3)
The network in ABC company is using the network address 192.168.1.64 with mask 255.255.255.192. In the network the servers are in the addresses 192.168.1.122, 192.168.1.123 and 192.168.1.124. An attacker is trying to find those servers but he cannot see them in his scanning. The command he is using is: nmap 192.168.1.64/28.
Why he cannot see the servers?
Correct Answer:C
https://en.wikipedia.org/wiki/Subnetwork
This is a fairly simple question. You must to understand what a subnet mask is and how it works.
A subnetwork or subnet is a logical subdivision of an IP network.The practice of dividing a network into two or more networks is called subnetting.
Computers that belong to the same subnet are addressed with an identical most-significant bit-group in their IP addresses. This results in the logical division of an IP address into two fields: the network number or routing prefix and the rest field or host identifier. The rest field is an identifier for a specific host or network interface.
The routing prefix may be expressed in Classless Inter-Domain Routing (CIDR) notation written as the first address of a network, followed by a slash character (/), and ending with the bit-length of the prefix. For example, 198.51.100.0/24 is the prefix of the Internet Protocol version 4 network starting at the given address, having 24 bits allocated for the network prefix, and the remaining 8 bits reserved for host addressing. Addresses in the range 198.51.100.0 to 198.51.100.255 belong to this network. The IPv6 address specification 2001:db8::/32 is a large address block with 296 addresses, having a 32-bit routing prefix.
For IPv4, a network may also be characterized by its subnet mask or netmask, which is the bitmask that when applied by a bitwise AND operation to any IP address in the network, yields the routing prefix. Subnet masks are also expressed in dot-decimal notation like an address. For example, 255.255.255.0 is the subnet mask for the prefix 198.51.100.0/24.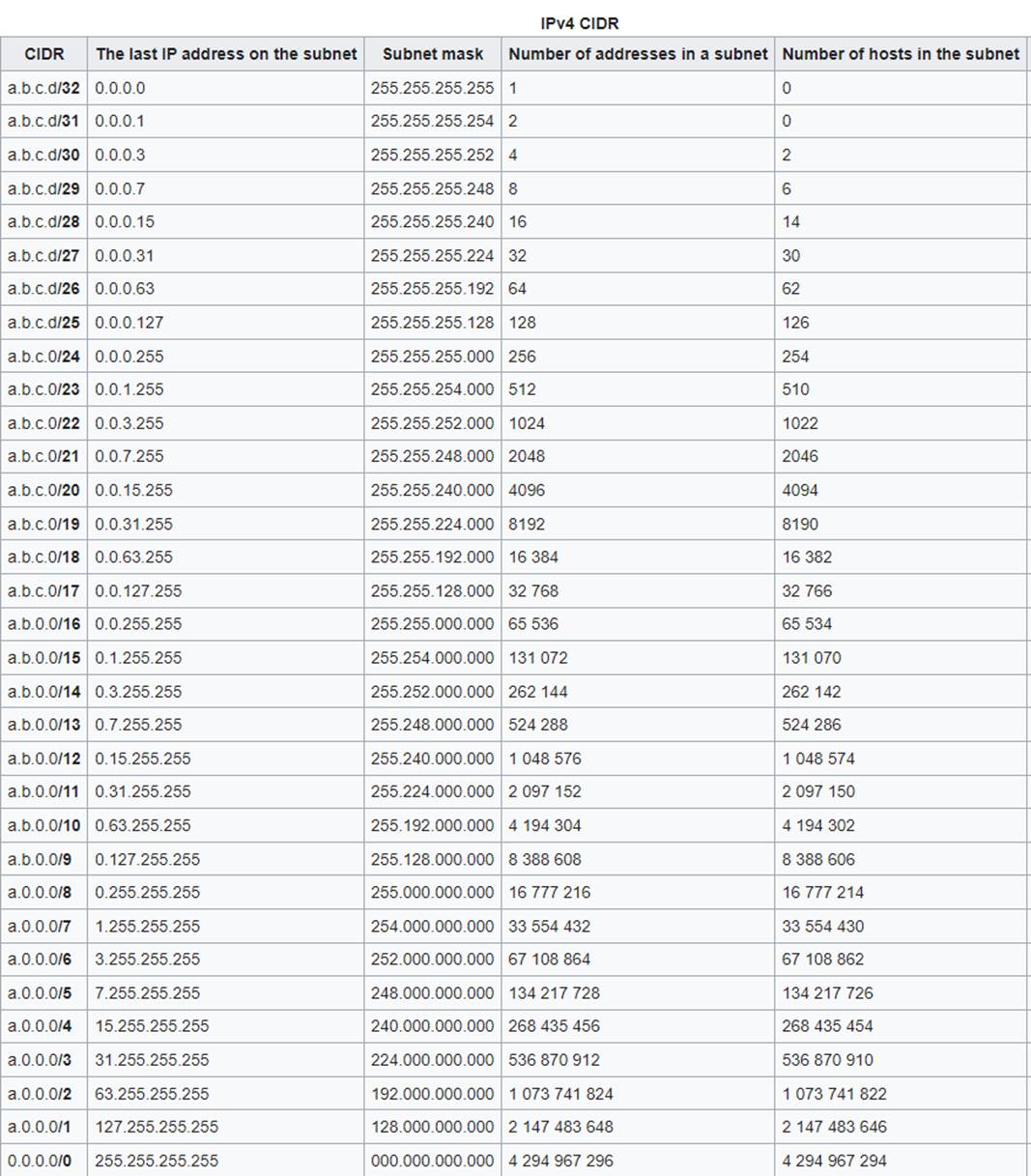
Table Description automatically generated