Question 7
You are asked to see if your persistent NAT binding table is exhausted. Which show command would you use to accomplish this task?
Correct Answer:D
The command show security nat source persistent-nat-table all provides a comprehensive view of all entries in the persistent NAT table, enabling administrators to monitor and manage resource exhaustion. Refer to Juniper NAT Monitoring Guide for more.
In Junos OS, when persistent NAT is configured, a binding table is created to keep track of NAT sessions and ensure that specific hosts are allowed to initiate sessions back to internal hosts. To check if the persistent NAT binding table is full or exhausted, the correct
command must display the entire table.
✑ Correct Command (D):
✑ Incorrect Options:
Juniper References:
✑ Juniper Persistent NAT Documentation: Describes the persistent NAT binding table and the commands used to monitor its status.
Question 8
A customer wants to be able to initiate a return connection to an internal host from a specific
Server.
Which NAT feature would you use in this scenario?
Correct Answer:A
Question 9
Referring to the exhibit, you have been assigned the user LogicalSYS1 credentials shown in
the configuration.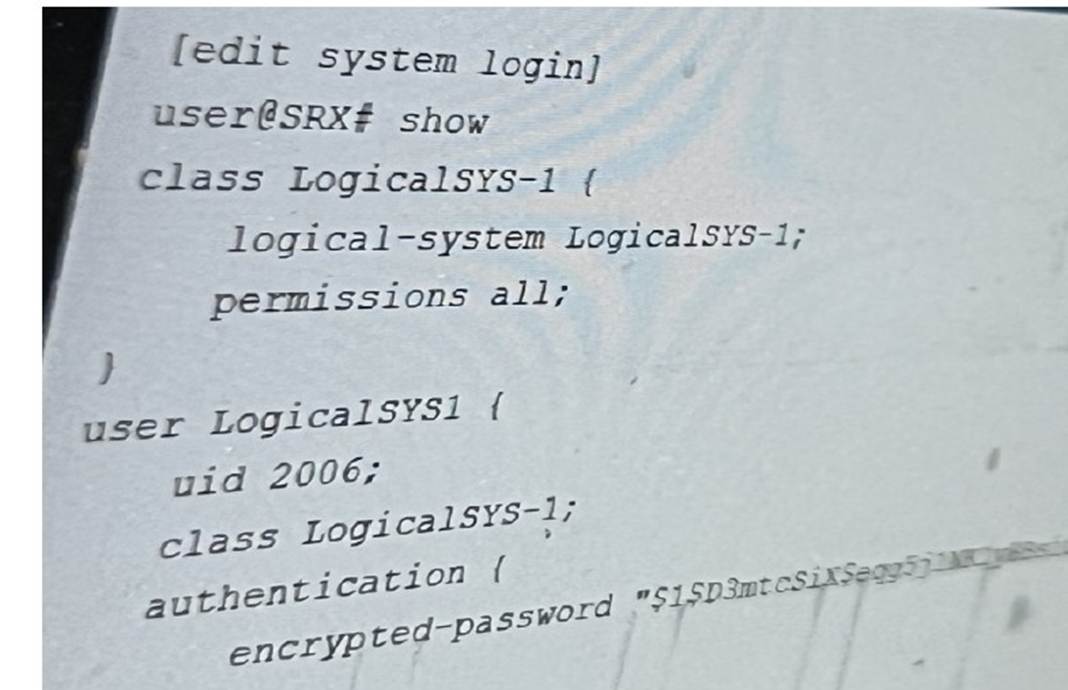
In this scenario, which two statements are correct? (Choose two.)
Correct Answer:BC
Question 10
How does an SRX Series device examine exception traffic?
Correct Answer:A
Exception traffic, including management and control plane traffic, is handled by examining host-inbound traffic configurations at the ingress interface and zone. It ensures traffic reaches necessary services like SSH and IKE securely. See Juniper Host Inbound Traffic Documentation for more.
SRX Series devices handle exception traffic (such as management traffic like SSH, Telnet, DNS queries, etc.) differently than regular transit traffic. Exception traffic is examined based
on host-inbound traffic for the ingress interface and zone. If traffic is destined for the device itself (e.g., management traffic or routing protocol messages), it must be allowed as host-inbound traffic on both the ingress interface and zone.
Example Command: bash
set security zones security-zone trust host-inbound-traffic system-services ssh
This ensures that traffic destined to the SRX device is inspected based on the ingress interface and zone.
: Juniper documentation on host-inbound traffic and exception handling.
==========
Question 11
You are configuring advanced policy-based routing. You have created a static route with next
hop of an interface in your inet.0 routing table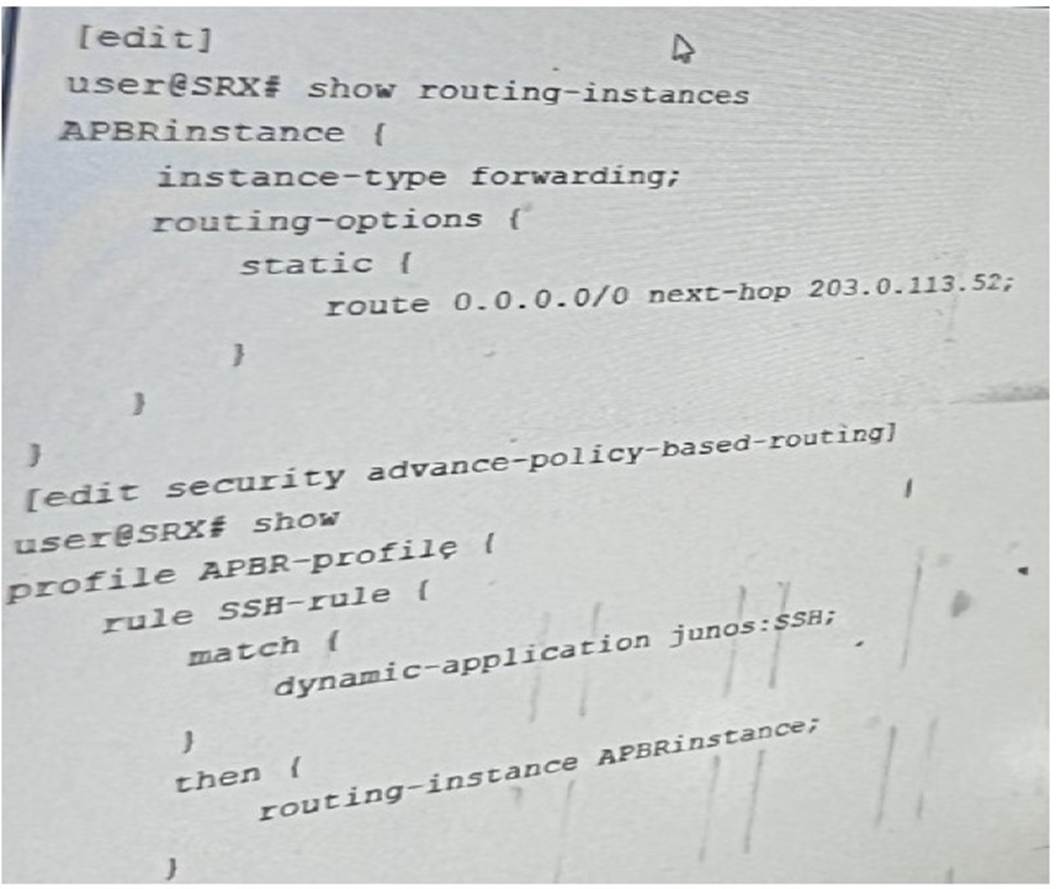
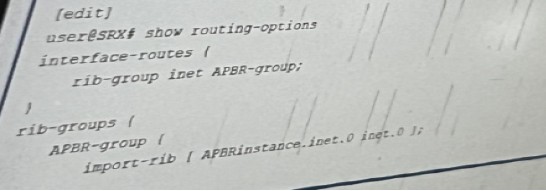
Referring to the exhibit, what should be changed to solve this issue?
Correct Answer:C
Question 12
You are using ADVPN to deploy a hub-and-spoke VPN to connect your enterprise sites. Which two statements are true in this scenario? (Choose two.)
Correct Answer:CD