Question 13
You have deployed automated threat mitigation using Security Director with Policy Enforcer, Juniper ATP Cloud, SRX Series devices, and EX Series switches.
In this scenario, which device is responsible for blocking the infected hosts?
Correct Answer:A
Policy Enforcer interacts with other network elements like EX switches to enforce blocking of infected hosts based on threat intelligence from ATP Cloud and other sources. For more information, refer to Juniper Policy Enforcer Documentation.
In a Juniper automated threat mitigation setup involving Security Director, Policy Enforcer, Juniper ATP Cloud, SRX Series, and EX Series switches, the Policy Enforcer is the component responsible for blocking infected hosts. The role of each component is as follows:
✑ Policy Enforcer (Correct: Option A):Policy Enforcer receives threat intelligence
from Juniper ATP Cloud and instructs SRX devices and EX Series switches to block or quarantine infected hosts. Policy Enforcer pushes policies to these devices to enforce the mitigation actions.
✑ Security Director (Incorrect):Security Director provides centralized management
and visibility but does not directly enforce policies.
✑ Juniper ATP Cloud (Incorrect):Juniper ATP Cloud is responsible for analyzing threats and providing intelligence but does not take direct mitigation actions.
✑ EX Series Switch (Incorrect):EX Series switches can enforce the policy pushed by Policy Enforcer but are not responsible for deciding which hosts to block.
Juniper References:
✑ Juniper ATP Cloud and Policy Enforcer Documentation: Details the roles of each component in the automated threat mitigation architecture.
==========
Question 14
Which two statements are correct about DNS doctoring?
Correct Answer:BD
Question 15
Click the Exhibit button.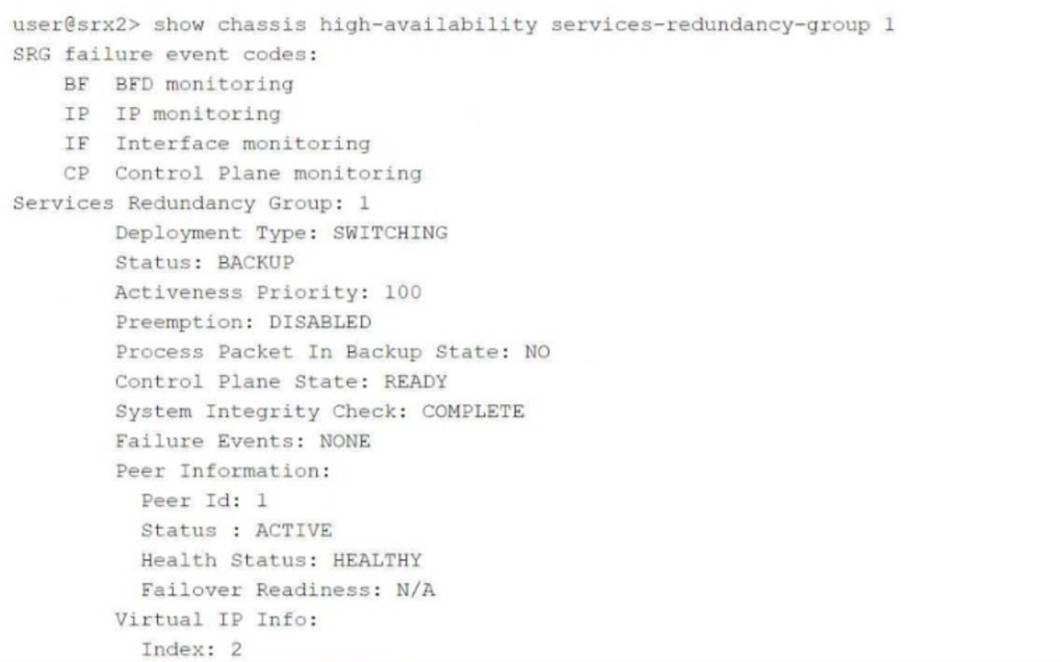
Referring to the exhibit, which two statements are correct? (Choose two.)
Correct Answer:CD
Question 16
Exhibit: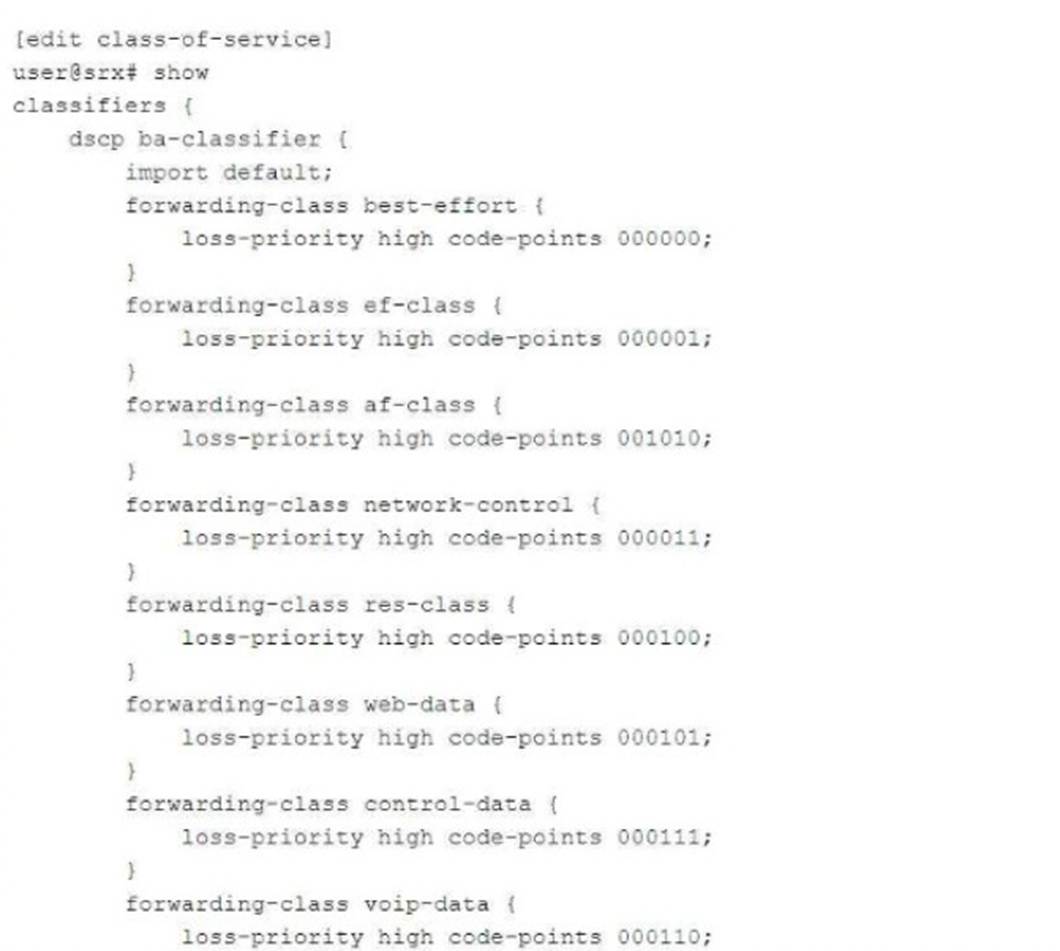
You have configured a CoS-based VPN that is not functioning correctly. Referring to the exhibit, which action will solve the problem?
Correct Answer:A
In the exhibit, the CoS-based VPN configuration is not functioning correctly due to an issue with the number of forwarding classes. The maximum number of forwarding classes supported for CoS-based VPNs with multiple SAs (security associations) is typically four forwarding classes. In this case, more than four forwarding classes are defined.
To solve the issue, one forwarding class must be deleted to ensure that the total number of forwarding classes is reduced to four or fewer.
: Juniper CoS-based VPNs and forwarding class limitations.
==========
Question 17
Click the Exhibit button.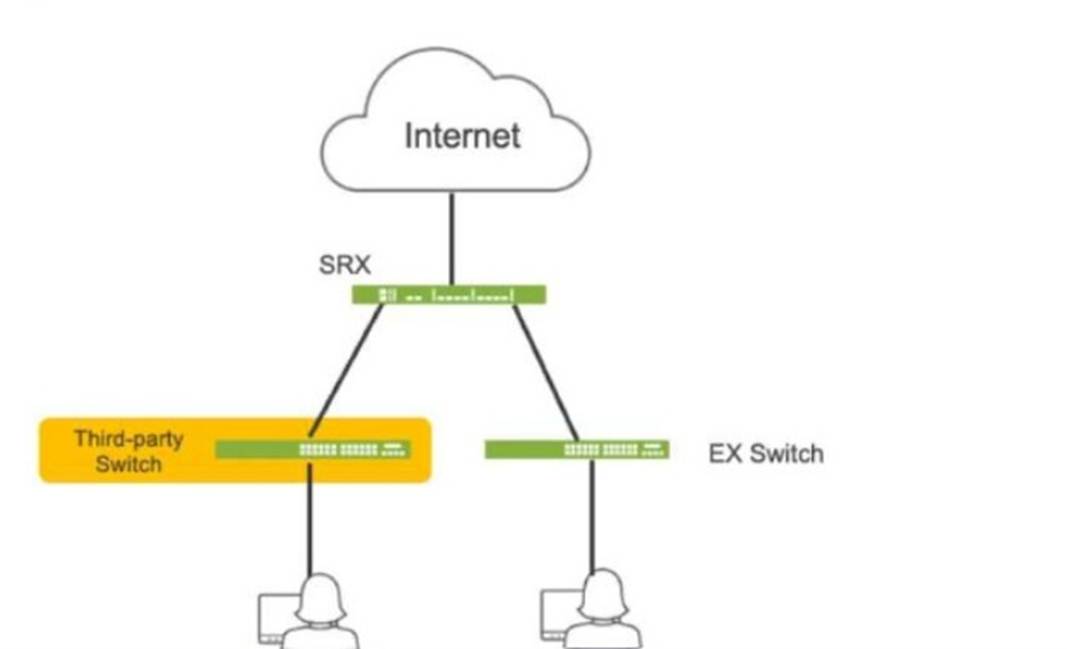
Referring to the exhibit, which three actions do you need to take to isolate the hosts at the switch port level if they become infected with malware? (Choose three.)
Correct Answer:ABC
✑ A. Enroll the SRX Series device with Juniper ATP Cloud. This is essential for the SRX to receive threat intelligence from ATP Cloud, enabling it to identify infected hosts and take action.
✑ B. Use a third-party connector. In this specific scenario, a third-party connector is required to integrate the SRX with the third-party switch. While Juniper has native integration for its EX switches, a connector is necessary to communicate with and manage the third-party switch.
✑ C. Deploy Security Director with Policy Enforcer. Security Director orchestrates the automated response, and Policy Enforcer translates the policies into device- specific commands for the SRX and the third-party switch (via the connector).
==========
Question 18
You are asked to configure tenant systems.
Which two statements are true in this scenario? (Choose two.)
Correct Answer:CD
Each tenant system maintains its own configuration database, isolating configurations from others, enhancing security and operational efficiency. Junos OS supports multiple concurrent commit operations across tenant systems. Further details are covered in the Juniper Tenant System Guide.
When configuring tenant systems on an SRX device, the following principles apply:
✑ Tenant Systems Have Their Own Configuration Database (Answer C): Each tenant system has its own isolated configuration database, ensuring that changes made in one tenant system do not affect others. This allows for multi-tenant environments where different tenants can have independent configurations.
✑ Commit Multiple Tenant Systems Simultaneously (Answer D): The system allows for multiple tenant systems to be committed at the same time, simplifying management when working with multiple tenants. This is particularly useful in large environments where multiple logical systems or tenants need updates simultaneously.
: Juniper documentation on tenant systems and configuration databases.
==========